Breaking Down The Big Business Of Fraud

Cybercriminals run their operations far more like legitimate businesses than we’d like to think. Most fraudsters are both well-organized and sophisticated, able to plan and execute attacks right under our noses. As part of our Anatomy of a Fraud Attack series with Kount, we’ll go inside the mind of fraudster to see gain better insight into the threat they pose.
Fraudsters always seem to be one step ahead of both the consumers and businesses they target.
They have the uncanny ability to slip in unnoticed, wreak havoc and essentially walk away unscathed (and paid). Though victims of fraud attacks may never be able to beat cybercriminals at their own game, it’s clear that knowledge is power.
As Don Bush, VP of Marketing at Kount, recently told Karen Webster, knowing what’s coming can better prepare you to defend yourself.
“If you don’t know what they’re doing, then you don’t know how to counteract,” Bush explained.
“We can give insight to what they’re doing to help you have a chance to slow them down, put multiple hurdles in their way and let them go on to easier targets.”
In this month’s installment of the Anatomy of a Fraud Attack series with Kount, we take a look at an increasingly favorite type of fraud among cybercriminals: carding or card testing.
By looking at things from the view of a fraudster, we’ll go into how these types of attacks are typically planned and executed …
Setting Up Shop
“I think you have to think of [fraudsters] just like other business people because it’s grown into that – this is no longer the little hacker that plays around on his computer. It’s usually pretty organized,” Bush explained.
Carding may not be a new technique, but with the wealth of data floating around from larger data breaches and huge databases of compromised payment card data, it’s becoming a new favorite.
The breaches that take place and financial records that become available as a result, the better chance we fraudsters have at finding, purchasing and using (or just reselling) those cards.
But the start of any good operation must begin with a good plan. Like any legitimate business out there, when putting a fraud operation in place we have to make sure the right partners, assets and even tools are available.
This takes research.
The onslaught of online blogs and chat rooms dedicated to hackers and our pursuits serve as a one-stop-shop for information and knowledge sharing. Never has it been so easy to connect and network with other cybercriminals, while also having access to the types of resources guaranteed to improve our own activities.
Whether it’s stealing and validating card data, selling stolen electronics on eBay or reselling event tickets, we all end up finding our way to our own fraud specialties. Think of it like deciding what area of business you want to work in or what topic you find most interesting to write about – it may take us some time to discover the area of fraud in which we truly shine.
Luckily for us, the internet offers access to training videos for almost any type of fraud we are looking to commit. There’s even so-called “internship programs” where we can try out different fraud areas to learn the ropes.
At the end of the day, no matter which type of method we use to perpetrate our crimes, we keep our eyes on the prize.
“Fraudsters don’t just want to make money, they want to turn what they do into cash as quickly as possible,” Bush emphasized.
Tools Of The Trade
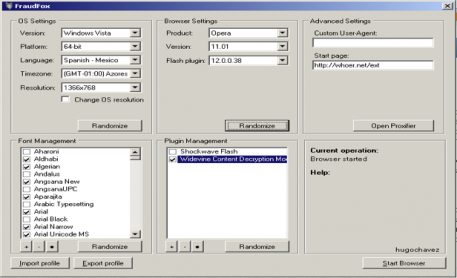
There’s no denying that the tools and technologies made available today make it easier than ever to execute fraud strategies.
These include tools to disguise an IP address, disguise an entire device, scan websites and databases to pull out data resembling passwords and IDs, as well as bots and Trojans that grab information and send it to a central repository.
 Just to name a few.
Just to name a few.
We are also flush with the right connections to keep our illicit businesses running – from retailers to wholesalers, or even our own Amazon, eBay or eCommerce stores. Having all the pieces in place make it easy to not only steal whatever digital or physical good we’re after, but also turn around and get it out the door as quickly as possible.
Bush likens it to the “bizarro world” concept mentioned in “Seinfeld.” Fraudsters are capable of having the same types of operations available to get a good or service out on the market just like any other legitimate business.
The Data Jackpot
“Data is valuable based on how much of it there is and how good it is and what types of applications a criminal wants to use,” Bush said.
Payment card data is always welcome to a fraudster, but with an estimated 600 million to 700 million accounts being compromised last year alone it’s become somewhat of a commodity in the hacker market.
It’s simple supply and demand. Stolen card data is everywhere and the price to purchase has dropped significantly.

But personal data is still considered quite a treasure.
With information about identities or other financial information we can do so much more than just make purchases online. Having a consumer’s digital identity opens the door to applying for a loan or other lines of credit, and doing more things with the data that will actually help me.
Personal data also has an advantage because unlike with compromised card data, consumers have started to slow down the speed in which they actually act on finding out the data has been stolen.
And we’ve gotten smart to that change in behavior.
Let’s say I purchase a million pieces of information on the dark web. Because consumers have gotten somewhat lazy about their security, I know that I can just hold onto it and instead use it later on when things have calmed down and they are less likely to notice.
Probably the most desirable piece of identity information comes in the form of IRS records.
They can tell us fraudsters everything – a person’s home mortgage, investments, salary, banking information, contributions and even all their identification information.
This allows us to spoof in a very sophisticated way, like sending an email from “XYZ Bank” about that new mortgage you just applied for but saying that some additional information is needed.
As Bush pointed out, “those are the things that really get you worried. It gets dangerous.”
A Golden Opportunity
“I think they’re always probing on what’s the next better deal,” Bush stated.
If it’s not broke, why fix it?
That should be the fraudster philosophy – we’re able to keep the fraud attacks going because the methods we are using are still working.
The reason you’re still getting emails from that “Nigerian prince” who wants to give you millions of dollars is because someone actually responded to the message with their bank account information.
But that doesn’t mean we aren’t always on the lookout for a new (and profitable) fraud opportunity.
It also helps that we don’t have to play by anyone’s rule, which makes it easy to not really fear getting caught.
Unfortunately for the “good guys” trying to track us down, they run into issues with determining who truly has the jurisdiction to chase fraud operations across state and international lines. Above that, who really has the expertise, resources and even manpower to lead the charge against any and every fraudulent activity?
The answer: not many.
“They don’t have to play by the rules but we do,” Bush explained.
You got that right!
