Intel Chips’ Hackability Problem Is Worse Than Initially Thought
Last week reports began to emerge that for the last seven years, Intel chips have contained an authentication bypass vulnerability that makes it relatively easy to remotely hijack entire fleets of computers without ever entering a password.
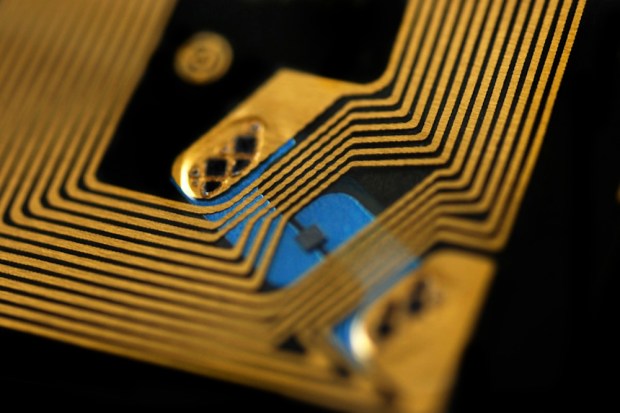
The authentication bypass vulnerability resides in an Intel chip feature known as Active Management Technology or AMT.
AMT is designed to give system administrators a large toolbox of powers executable over a remote connection. For example, from within AMT it is possible to change the code that boots up computers; access the computer’s mouse, keyboard, and monitor; load and execute programs; and remotely power on computers that are turned off.
Basically, with access to AMT, a remote users gets all the power and control over a system that a physically present network administrator would have.
One might assume that such a power set of capabilities would be very locked down — and the system was apparently designed to require a password before remote access would be granted via a web browser.
One problem, though — as it turns out, authentication can be bypassed pretty easily. Entering any text string — or no text at all — is sufficient to push into the system.
According to a blog post published Friday by Tenable Network Security: “Authentication still worked,” even when the wrong hash was entered, Tenable Director of Reverse Engineering Carlos Perez wrote. “We had discovered a complete bypass of the authentication scheme.”
Embedi, the security firm Intel credited with first disclosing the vulnerability, arrived at the same conclusion in a separate technical analysis.
And if that sounds bad, it gets worse. Unauthorized accesses typically aren’t logged because AMT has direct access to the computer’s network hardware. That means when AMT is in use, all network packets are redirected to the Intel Management Engine and from there to the AMT. Those network packs never hit the OS at all. So if a system were hacked by this method, the hack would be rather tough to find.
And these chips have been out on the market in some — but not all — Intel chipsets since 2010.
Intel officials expect PC makers to release a patch next week, according to a blog post last week. The releases will update Intel firmware.
According to reports in ArsTechinca, the Shodan security search engine found over 8,500 systems with the AMT interface exposed to the Internet, with over 2,000 in the United States alone.
