Cybersecurity
Source: en.wikipedia.org
Bitcoin Bewilderment Tubes WannaCry’s Hacker Haul

Was North Korea Behind WannaCry Ransomware Attack?
May 16, 2017 | Security & FraudThe hackers behind the WannaCry ransomware attack that has created havoc around the globe is still a mystery, but one researcher thinks it’s Lazarus Group,...
READ MORE >

When Machines Do The IDV Work Of People
May 16, 2017 | PodcastIndustries are abuzz with the fast-growing potential of machine learning — a form of artificial intelligence that allows programs to change, adapt and, obviously, learn...
READ MORE >

SWIFT Urges Cybersecurity Info Sharing With New Portal
May 16, 2017 | B2B PaymentsWith FIs still reacting to last year’s series of cybersecurity attacks, during which hackers infiltrated banks via their connectivity to the SWIFT network, SWIFT has...
READ MORE >
Today in Data: Global ‘WANNACRY’ Cyber Attack Impact
May 15, 2017 | Security & FraudCyber attacks have been impacting organizations all around the world recently, with Friday’s ‘WANNACRY’ ransomware attack hitting businesses from all sectors, globally, especially hard. From...
READ MORE >

FTC Cracks Down On Tech Support Scams
May 15, 2017 | Security & FraudThe U.S. Federal Trade Commission (FTC), in conjunction with other federal, state and international law enforcement partners, recently announced a nationwide and international crackdown on...
READ MORE >

Keeping Third Party Risk First On The Cyber (Risk) List
May 15, 2017 | NewsAs companies expand and interact with an ever-widening web of vendors, third-party risk deepens as data is shared and, potentially, exposed. In the latest Topic...
READ MORE >

Trump Signs New Executive Order On Cybersecurity
May 12, 2017 | Security & FraudU.S. President Donald Trump on Thursday (May 11) signed an executive order that seeks to increase cybersecurity efforts on the part of the government, with...
READ MORE >
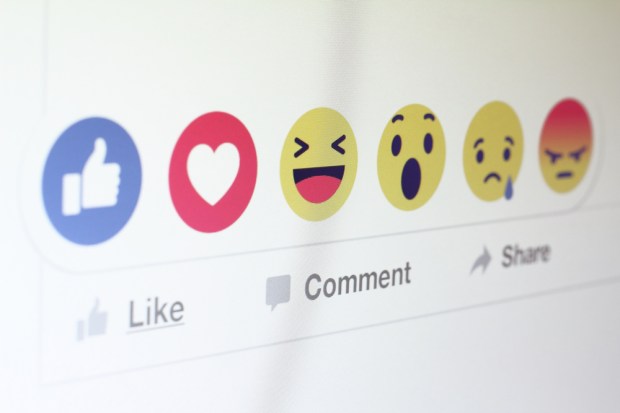
Stolen Card And Loyalty Credentials For Sale On Facebook Says LFPA
May 12, 2017 | FacebookThe newly formed Loyalty Fraud Prevention Association (LFPA), launched in September of last year, has made a bold claim in its latest release. Get the Full...