SamSam Ransomware Attacks Are On The Rise
SamSam ransomware attacks are up — and the attackers are getting more demanding.
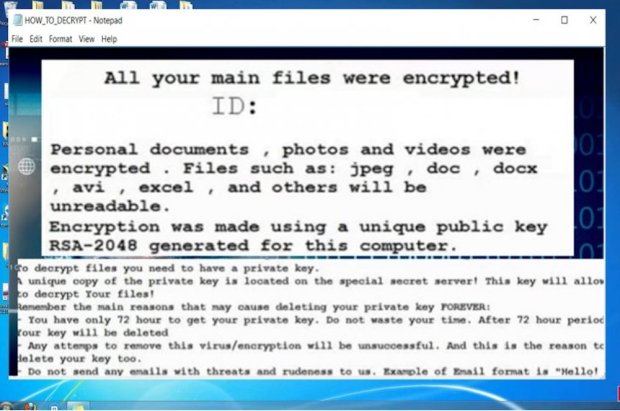
The normal demand for decrypting one’s files is a few hundred dollars, in return for which victims get back access to their hijacked computers. But the folks behind SamSam have decided to think bigger and are asking for far more.
Written in C#, the malware goes after a particular unpatched server vulnerability — and according to experts, the hackers behind it are still learning the extortion game. Currently the malware has caught the FBI’s attention.
“MSIL or Samas.A (SAMSAM) was used to compromise the networks of multiple U.S. victims, including 2016 attacks on healthcare facilities that were running outdated versions of the JBoss content management application,” the FBI says. “SamSam exploits vulnerable Java-based Web servers. SamSam uses open-source tools to identify and compile a list of hosts reporting to the victim’s active directory.”
“The actors then use PsExec.exe to distribute the malware to each host on the network and encrypt most of the files on the system,” the FBI added. “The actors charge varying amounts in bitcoin to provide the decryption keys to the victim.”
Researchers at AlienVault noted that this ransomware also has a talent for spreading to any computers that share a network with the infected computer. The ransomware has also been recently updated to personalize the experience of being hacked by charging different amounts depending on how bad the infection is.
If one machine has been infected, 1.7 bitcoin, or about $4,600, is the price. If more machines are locked by the ransomware, half will be decrypted for 6 BTC or $16,400 — or one can buy in bulk and shell out 12 BTC, or $32,800.
Last week did see $33,000 being paid to a bitcoin wallet associated with SamSam.
SamSam is not known as a particularly advanced piece of malware — though it is an effective one. An NYC hospital was extorted to pay $44,000 to SamSam operators or lose access to its systems after a successful infection. The hospital, incidentally, said no — and endured a month of disruption before the hospital’s systems were restored.