Deep Dive: GDPR And The EU’s New Rules Of Data Handling

On May 25, 2018, the EU-wide mandate known as the General Data Protection Regulation (GDPR) will take effect. Once the law goes live, companies that operate in the EU can face heavy fines or sanctions for mishandling personal data of customers, clients or employees. This PYMNTS Deep Dive examines the origins of the GDPR mandate and what the new requirements will mean for businesses of all sizes.
Earlier this month, the world watched as Facebook CEO Mark Zuckerberg faced an intense barrage of questions from U.S. lawmakers about how his company can better protect its users’ data following the Cambridge Analytica breach. The social media platform has admitted the incident may have impacted as many as 87 million users.
During the exchange, lawmakers raised the specter of regulating Facebook — which boasts more than 2.2 billion worldwide users — including legislation that would require it to obtain opt-in consent from users to use, share or sell any personal data. While such a move might be unprecedented in the U.S., similar regulations are already being put to the test in other regions around the world.
Understanding that the brave new world of connectivity also creates a set of challenges, the European Commission has begun outlining guidelines for companies in the space and promoting heightened cybersecurity to keep citizens’ personal data safe. The guidelines were equally prompted by rapid social media growth, globalization and technology penetration, all of which have made it easier for personal information to be accessed or exchanged.
European Union (EU) officials have recognized that individuals and businesses in member states are eager to join the digital economy. Shortcomings in underlying IT networks and components can leave millions of users’ personal data exposed, however. As such, EU leaders began looking for solutions that balanced the need to protect personal data with encouragement of greater digital economy participation.
That effort kicked off in 2012, when the European Commission first began taking steps to advance data protections in the EU. Four years later, the Commission has reached an agreement on which rules to include in reforms and also how they will be enforced.
Among the most significant reforms was the General Data Protection Regulation (GDPR), an EU-wide mandate to strengthen the protection measures impacting EU citizens’ personal data and privacy. Under the GDPR, which is scheduled to take effect on May 25, heavy fines can be imposed on companies that fail to comply with the guidelines or to authorize EU agencies to enforce the regulations.
Advertisement: Scroll to Continue
The following Deep Dive examines the GDPR’s origins, its expected long-term effect on the EU’s data protection culture and the new requirements businesses of all sizes must meet when handling the personal data of customers, clients and employees.
GDPR 101
The GDPR affects any company or organization that operates, stores or processes personal data belonging to EU citizens, defined as “any information relating to an identified or identifiable natural person (data subject).”
Enforcement of GDPR laws will fall to the Data Protection Authorities (DPAs) across the EU. DPAs are independent public agencies that have been granted “investigative and corrective powers” to ensure GDPR requirements are being met. Each EU member nation has a DPA in place to both monitor compliance and respond to potential violation complaints.
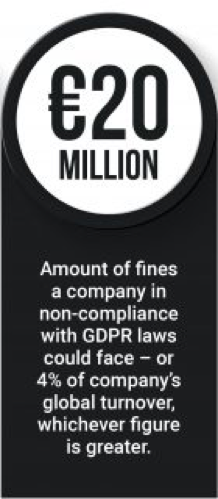
The penalty for non-compliance is expected to be severe once the GDPR takes effect. According to the directive, the DPA may investigate the case if a complaint is lodged against an active EU company or if a DPA suspects a company is not in compliance. If it determines the organization has failed to comply with the new rules, the DPA can impose a fine up to €20 million ($24.7 million USD) or 4 percent of the company’s global worldwide turnover, whichever is greater.
Even if fines are not issued, other aggressive actions may be levied against non-compliant businesses. DPAs can suspend or restrict how much data is transferred to the U.K. once it leaves the EU, impose a temporary or definitive ban on a company’s ability to process data, reprimand the company or issue warnings and order rectification.
The GDPR framework will be applicable to all EU member states, and will supersede the rules currently in place under the existing, 20-year-old Data Protection Directive 95/46/EC. That directive’s rules became cumbersome, costly and confusing over time as EU-based businesses struggled to address 28 different data protection laws. The previous regulations’ fragmented nature also made it difficult for companies — especially SMBs — to access new markets as they did understand with which laws they were required to comply.
 Among the most significant GDPR components is the need for enhanced authentication. The EU’s Agency for Network and Information Security (ENISA) noted that usernames and passwords are no longer sufficient tools to protect users’ personal data. The key to strengthening the authentication process, then, is securing computer systems and introducing greater security at remote services and facilities. One-time passwords are considered GDPR-compliant authentication solutions, as are smart cards and FIDO Alliance Universal 2nd Factor (U2F).
Among the most significant GDPR components is the need for enhanced authentication. The EU’s Agency for Network and Information Security (ENISA) noted that usernames and passwords are no longer sufficient tools to protect users’ personal data. The key to strengthening the authentication process, then, is securing computer systems and introducing greater security at remote services and facilities. One-time passwords are considered GDPR-compliant authentication solutions, as are smart cards and FIDO Alliance Universal 2nd Factor (U2F).
The GDPR framework will be applicable to all EU member states, and will supersede the rules currently in place under the existing, 20-year-old, Data Protection Directive 95/46/EC. That directive’s rules became cumbersome, costly and confusing over time as EU-based businesses struggled to address 28 different data protection laws. The previous regulations’ fragmented nature also made it difficult for companies — especially SMBs — to access new markets as they did understand with which laws they were required to comply.
Among the most significant GDPR components is the need for enhanced authentication. The EU’s Agency for Network and Information Security (ENISA) noted usernames and passwords are no longer sufficient tools to protect user’s personal data. The key to strengthening the authentication process, then, is securing computer systems and introducing greater security at remote services and facilities. One-time passwords are considered GDPR-compliant authentication solutions, as are smart cards and FIDO Alliance Universal 2nd Factor (U2F).
Assessing Risk for SMBs
Keeping smaller businesses in line is of particular concern when it comes to GDPR compliance. Some estimates indicate that SMBs make up more than 95 percent of global businesses, but these businesses often do not have the resources to invest in GDPR compliance.
These SMBs will have to fulfill certain legal obligations under GDPR, including taking on the data controller role, which can entail processing customers’ or employees’ personal data. SMBs sometimes engage in data processing by providing data services to customers on another company’s behalf. This involves data collection, storage, use, transfer and disposal, among other functions.
GDPR requires that all businesses take a risk-based approach to handling personal data. The greater the risk, the more rigorous requirements the data controller or processor must meet to keep the data secure, according to the regulations.
ENISA urges organizations to define the boundaries of their data processing systems and the relevant context. Understanding these parameters can help businesses further understand the impact that a potential security incident — such as a data breach or theft — could bring. Organizations should assess how breaches could impact the rights and freedoms of affected individuals, ENISA said, as well as the likelihood of such an event and the ultimate level of risk.
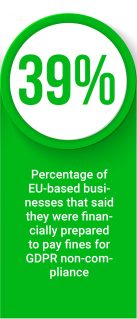
To date, only a handful of EU-based organizations have said they are ready for the impact of such a breach. A recent report found just 39 percent of businesses were financially prepared to pay the fines related to GDPR non-compliance, and 24 percent had purchased cyber insurance. Those numbers could increase as more companies develop a deeper understanding of potential GDPR non-compliance risks, however.
At least one company outside the EU is already making its GDPR-compliance strategy known. A spokesperson for U.S.-based Gift Baskets Overseas, which ships gifts to overseas markets, recently told digital news site MarTech Today that it is communicating to customers that data collection is needed for order processing and will only be stored for a limited time. It is also making a point of contact available to users and authorities through its website, ensuring that issues related to data, security, removal and extraction requests are addressed.
Authentication as a Basic Security Measure
ENISA suggests that companies invest in stronger authentication and access control safeguards to stay GDPR-compliant. In other words, companies must have a strong understanding of exactly who can access the personal data the organization is handling.
According to ENISA, it is recommended to keep a log of the system administrators responsible for monitoring users that engage with a company’s IT system. Those administrators should track who can create, approve, review and delete user accounts, and should avoid accounts that are shared or common. If such accounts are needed, however, the group recommends that all common account users are held to the same roles and responsibilities.
ENISA advises organizations to implement an authentication mechanism to enable access to the organization’s IT system. At a minimum, a username and password should be required to access the system, with passwords adhering to a certain level of complexity. That access control panel should be able to detect and deny passwords that do not meet the necessary complexity threshold. Allowable passwords should be defined by appropriate length, complexity, validity period and number of acceptable unsuccessful login attempts, and be stored in “hashed” form.
Additional ENISA recommendations include adopting two-factor authentication to access systems that process personal data, including passwords, security tokens, USB drives with secure tokens or biometrics. As mobile devices are likely to be used for personal purposes, they can also increase data theft risks, the group added. Additional steps must be taken to ensure that business-related data is not compromised. It urges two-factor authentication to be used to access mobile devices and that personal data stored on those devices to be encrypted.
The Need for Greater GDPR Compliance
In addition to Zuckerberg’s grilling on Capitol Hill, the Federal Trade Commission (FTC) also recently launched an investigation into Facebook. The social media giant’s woes are only the latest chapter in an ongoing series of cyber breaches impacting the personal data of millions, however.
Recent history indicates data breaches are becoming more common — and more severe. Last year’s Equifax breach resulted in the exposure of more than 145 million Americans’ personal data. Cyber criminals also unleashed the WannaCry ransomware attack that infected 200,000 computers in at least 150 countries.
 A recent survey indicates that IT professionals believe the pattern is likely to continue, which spells serious trouble for companies doing business in the EU. A survey of 1,500 IT professionals found that 64 percent suffered a data breach at least once in the past two years, and 100 percent reported that those breaches included personal data.
A recent survey indicates that IT professionals believe the pattern is likely to continue, which spells serious trouble for companies doing business in the EU. A survey of 1,500 IT professionals found that 64 percent suffered a data breach at least once in the past two years, and 100 percent reported that those breaches included personal data.
Given the current rate of breaches, roughly two-thirds of European businesses could be subject to fines under GDPR. This finding ramps up pressure to ensure companies’ data-handling practices are up to the new standards.
Companies should work to adopt a GDPR-compliant strategy for data handling to avoid consequences. That strategy should include ensuring apps are stored in a centralized data center or cloud-based environment; that security measures are enacted each time data is distributed or used offline; the development of context-aware policies based on user identity, device, location and network; and investment in analytics to quickly detect threats and reduce potential data risks. Companies should also consider performing a data inventory to better understand where information is stored, how it was acquired, who can access it and more.
In serious cases, however, companies may need to take more serious steps.
For example, certain EU nations may require organizations to appoint a data protection officer or assemble a data protection team. These roles may also be required if organizations are routinely engaged in large-scale monitoring or processing of large volumes of personal data.
As May 25 approaches, companies active in the EU must carefully assess whether their data-handling strategies are GDPR-compliant. While the looming deadline has some organizations scrambling, others see it as an opportunity to boost their profiles and win over customers by setting themselves apart from the competition. Companies that can demonstrate strong GDPR compliance strategies can stand out as more reliable, while others in the space fall short.
In an age in which cyber threats are rampant, companies that clearly demonstrate that they take data protection seriously may have a competitive edge in winning over consumers’ trust.
Download the latest issue of the Digital Identity Tracker™ to read this month’s feature story and get the latest headlines in the Digital Identity space.
About the Tracker
The Digital Identity Tracker™, sponsored by Jumio, is a forum for framing and addressing key issues and trends facing the entities charged with efficiently and securely identifying and granting permission to individuals to access, purchase, transact or otherwise confirm their identities.