Robots. What could possibly go wrong?
Aside from being the starting question for roughly half the science fiction ever written, this is more recently also becoming a very real-world concern as security issues are popping up in the robotics that are becoming an increasingly large part of consumers’ lives.
According to a report to be released Wednesday by IOActive, security flaws of note were found in an examination of six home and industrial robots. The report does not detail specific flaws, and instead focuses on categories of observable vulnerabilities.
“It’s important to note that our testing was not even a deep, extensive security audit, as that would have taken a much larger investment of time and resources,” the authors wrote. “The goal for this work was to gain a high-level sense of how insecure today’s robots are, which we accomplished.”
Stationary home robotics systems — like Amazon’s Echo or Google’s Home units — are the most visable parts of a rapidly expanding ecosystem of connected devices like doorbells, light bulbs and video cameras that consumers are just sort of assuming are secure.
Except, the reserach indicates, most manufacturers do not have good security practices, or infrastructures to deal with vulnerability reports or customers service around security issues.
Advertisement: Scroll to Continue
Moreover, the report notes, robots are moving toward becoming more autonomous and mobile — and self driving cars will just be one expansion of robots that can move freely in unstructured environments.
“We call it an internet-of-things with arms and legs and wheels,” said Cesar Cerrudo, chief technology officer of IOActive. “The surface of attack is huge. Each robot has multiple ways it can be compromised.”
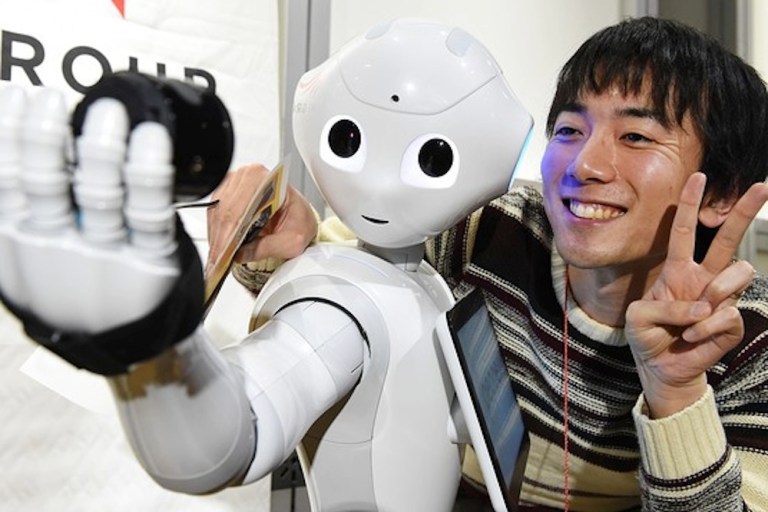
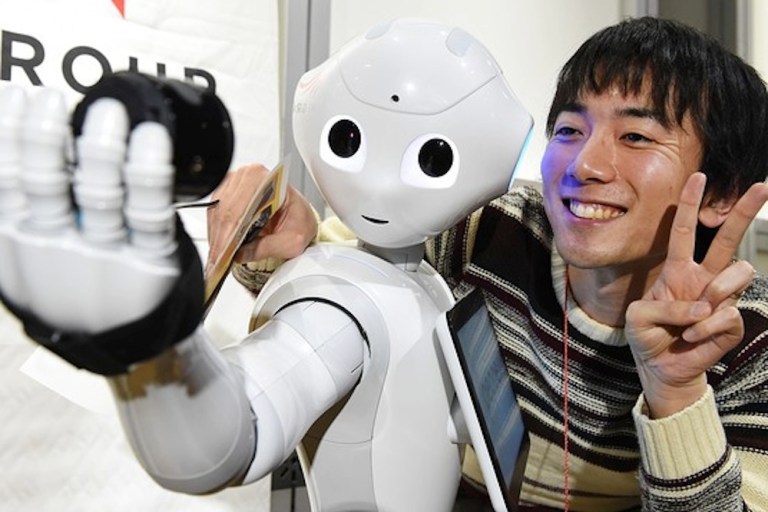
“Vendors like to add features that please the public,” said Lucas Apa, a senior security consultant at IOActive and one of the authors of the report. “They forget about important issues. Robots can have microphones and cameras; they can walk and they can grab objects. People don’t realize the consequences of something that can grab an object or can hear or see you.”
The report identifies seven different kinds of security issues, ranging from weak cryptographic systems and vulnerable default configurations to what security experts call authentication issues.
Robotic core function, it was found, in some cases could be controlled nearly entirely without authentication.
“We found key robot services that didn’t require a username and password, allowing anyone to remotely access those services,” the report said.
Of the six firms contacted in connection with the report — one has disputed the findings, one has noting it is “looking into it,” and four have not responded at all.