Say Hello To The New Kids On The Fraudster Block

It’s natural to worry about teens acting reckless on the roads when they first get their driver’s license or even skipping school, but what about hacking into your POS system? Yes, that’s right. Many we consider to be the “hope of the future” are actually budding fraudsters. Gilit Saporta, fraud analyst at Forter, told Karen Webster all about the teenage fraudster demographic and why merchants may want to steer clear.
We all know teenagers have a tendency to be a bit rebellious.
While some may be skipping school or making prank calls, there’s a growing demographic of teenagers out there with a new, more illicit hobby.
Fraud.
When it comes to fraudsters it’s easy to think of them as a faceless, nameless group of cybercriminals that come out to wreak havoc on payment systems and then retreat back to the hidden corners of the dark web.
But that’s just not the case.
Different segments of fraudsters have very different personas and motivations behind the activities they do.
In the new Fraudster Profile Podcast Series, Karen Webster is joined by Forter fraud analyst Gilit Saporta, who helps us to identify and break down the characteristics and personas within the diverse and ever-growing group of cybercriminals.
The latest installment focuses on a very surprising segment: teen fraudsters.
Just Teens Being Teens?
“With teenagers, we don’t believe that these guys are thinking of themselves as fraudsters to begin with,” Saporta explained, noting that in many cases teens may be exhibiting fraudulent behaviors but just see it as messing around or having fun.
Many teenagers today own smartphones and have an internet connection, so they essentially have the world in the palm of their hands.
With this type of access, they can quickly and easily take up what they think to be a “cool pastime,” such as using stolen credit card credentials to make purchases from their favorite game or seeing how many pizzas they can order before anyone notices.
And surprisingly, teenage fraudsters don’t always fit the mold of a thrill-seeking individual with highly sophisticated computer skills.
Saporta said that oftentimes the fraud attempts of teenage fraudsters take place with stolen card information that they may have picked up from a friend at school or perhaps a family member’s credentials.
“Sometimes you even see teenagers who aren’t that tech-savvy, but more often they have strong social media skills,” she added.
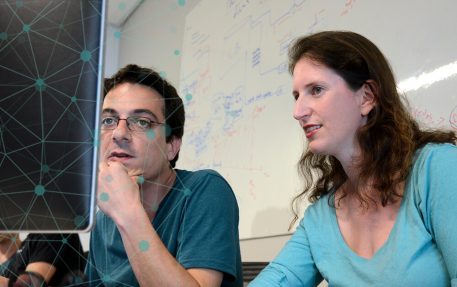
Gilit Saporta , Fraud Analyst, Forter
The Cyber Hierarchy
Though the threat posed by teen fraudsters places them on the lower end of the cybercriminal totem pole, the abundance of resources and support from the organized cyber ecosystem can still make them a problem for merchants.
What may be a prank or a game to a teen, still has the potential to cause harm to both merchants and customers alike.
And when these teenage fraudsters mature and decide to take their fraud activities more seriously, Saporta explained, they can certainly become more dangerous.
But the riskiest aspect of teen fraudsters is the fact that their activities can be very difficult to detect.
As Saporta pointed out, it can be hard to differentiate between the legitimate customer who just happens to be a teenager with consent to use a parent’s funding source, versus a teenager who is using a stolen credit card.
In many cases, teens committing fraud may not even realize their activities are fraudulent so they don’t bother to cover their tracks. On the flip side, those who are intentional in their fraudulent activities typically try to get creative when it comes to covering up their crimes, Saporta explained.
It’s not uncommon to see a teenage fraudster using pretty recognizable names – such as William Shakespeare, Justin Timberlake or even Kanye West – which may show they aren’t seriously trying to disguise themselves but may just view the fraudulent transaction as a gag, she added.
Putting Teen Fraudsters To Bed
Though Saporta couldn’t go into too much detail about Forter’s techniques for detecting and shutting down fraud perpetrated by teens, she did share what’s important to keep in mind when seeing these types of activities.
The first step for analysts to differentiate between the legit behavior and the fraudulent behavior of teens is to try to walk a mile in the fraudster’s shoes and to really picture themselves as that teenager looking to commit fraud, intentionally or unintentionally.
Saporta said that while seeing fraud committed at the teenage level is not a new phenomenon, it is one that continues to evolve and grow.
Over the last five years in particular, she’s noted that teens are moving from simply using family members as a source for stolen credit cards to going online to find stolen credentials.
It’s no wonder this trend has emerged, especially with the onslaught of data breaches in recent years that have made compromised payment data more accessible than ever before.
Whether teenage fraudsters grow up to become full-fledged cybercriminals or simply grow out of the rebellious fraudster phase is something that really can’t be generalized, but Saporta noted that the fraud attempts that used to be very easily characterized as coming from teens have continued to evolve to the next level.
It seems as though the well-oiled cybercriminal machine is working a little too well.
But, there’s always a silver lining.
“The good news is that it means many of the fraudsters are going to be demonstrating fairly similar behaviors and tactics,” Saporta pointed out, adding that this means there is also a pattern of bad behavior and good behavior that theoretically can be differentiated and tackled.
