When Hackers Outsmart The Smart Fridge
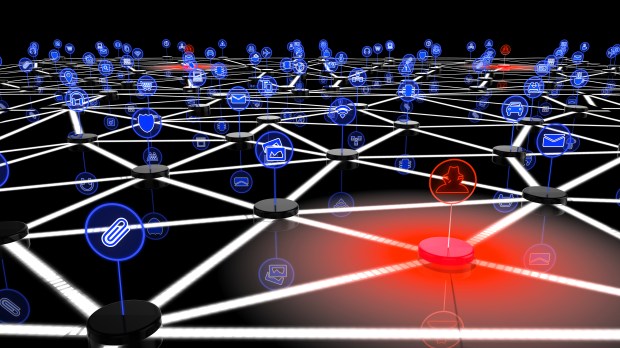
Cybercrime isn’t always about stealing credit card data. In the digital world, there’s strength in numbers, and a botnet — essentially, an army of IP addresses — can turn a pretty penny on the darknet. That’s why hackers are targeting Linux systems, and consumers don’t even know they’re using them.
While few computer users opt for a Linux operating system, almost every consumer has an Internet of Things (IoT)-enabled device (or 10) that runs on it, from webcams and DVRs in the home to point-of-sale terminals and ATMs in businesses. Even a smart refrigerator can be co-opted for criminal uses and, most of the time, the owner could never tell.
“If I have a botnet on your computer, my goal is not to let you know — I want to be able to use your computer whenever I want it,” said Corey Nachreiner, CTO of Seattle-based internet security company WatchGuard.
WatchGuard just released its quarterly Internet Security Report which showed that four out of the top 10 malware threats last quarter were Linux-based.
Linux Malware Threats
Linux-based threats showed up in a few forms. First, there’s the Trojan executable that takes over a device and offers a backdoor for the hacker. There’s the flooder which builds and leverages a botnet to carry out a distributed denial of service (DDoS) attack by overloading an enemy’s website with traffic. Finally, there’s the Linux downloader, which installs Linux malware on a victim’s computer.
“Hackers don’t care about spoiling your food,” said Marc Laliberte, an information security analyst at WatchGuard and co-author of the Internet Security Report. “Having any system is a resource. These IoTs become the beachhead. Then the hacker can go after the devices he really cares about.”
The Mirai malware is a recent, dramatic example of what a hacker can do with a botnet. Mirai exploited vulnerabilities in off-the-shelf, unencrypted Linux — something “no admin would knowingly expose to the internet,” said Laliberte.
In September 2016, the botnet attacked computer security journalist Brian Krebs’s website by hitting it with as many as 665 gigabits of traffic per second — nearly twice the size of the largest attack engineers had previously seen — but Akamai engineers were able to fend off the attack.
Later that month, the threat actor behind Mirai released the source code for the botnet so that other hackers could spread its infection even further, and the infection forked into several strains.
In October, a hacked army of Linux DVRs, security cameras, routers and smart fridges succeeded in crashing a variety of the internet’s top Dyn-powered destinations. Remember the day Twitter, Amazon, Tumblr, Reddit, Spotify and Netflix all stopped working? That was Mirai.
Cybercriminals can put their botnets up for rent so that fellow cybercriminals can flood enemies, monetize them by clicking on paid advertisements hundreds of thousands of times, or mine bitcoin.
Nachreiner and Laliberte said that IoT devices running an invisible Linux system are easy to exploit because their manufacturers want to push them out quickly and with little expense, so they don’t put as much effort into security as the average Linux administrator.
The reason for the skyrocketing attacks is simply the copycat effect. Once the Mirai hacker released the source code, people realized the big insecurity in IoT devices and started clamoring to take advantage.
Failure Of Legacy Antivirus Software
WatchGuard’s Internet Security highlighted another concerning trend that consumers would do well to note. Legacy antivirus software has been missing more and more threats, as many as 38 percent.
That’s because legacy antivirus looks for patterns, or “signatures,” of known malware. When a new piece of malware is discovered, antivirus programs add its signature to their checklists. But cybercriminals have been re-packaging malware using binary level techniques that jumble up the information on a digital level, even though it’s the same infection. The jumbled code doesn’t contain the signature that legacy antivirus recognizes, so it slips through the defenses.
Signature-based detection made sense once upon a time. It’s faster. But today, it’s missing more than a third of threats. The number of unique malware strains is growing exponentially, and legacy antivirus software just can’t keep up with all 80 million variants. Legacy antivirus usually misses new ransomware the day it comes out, then learns to recognize its signature over the next week or two.
Nachreiner said the slow failure of legacy software isn’t a new problem.
“This battle has actually been happening for the past five years to a decade, but it’s just now coming to light,” said Nachreiner. “Legacy antivirus has been missing malware for a while. Ransomware declares itself, but most malware is silent.”
WatchGuard’s Solution
WatchGuard began 21 years ago as a network security company focused on creating proxy-based firewalls. Today, a firewall isn’t enough: it looks at the envelope but doesn’t study what’s inside.
The company has now transformed from just building firewalls to offering unified threat management — what Nachreiner called a “next-generation firewall.” It now offers antivirus, web categorization, app control, intrusion prevention, data loss prevention and more, and has 550 employees stationed at offices all over the globe.
The information in the quarterly Internet Security Report is collected from WatchGuard customers who opted into the “Firebox Feed.” No personal data is collected; WatchGuard simply looks to see which types of viruses are prevalent and which regions are most threatened by them.
Nachreiner said the main takeaway of the report is defense. “Attacks are evolving,” he said. “Be suspicious. There are simple things people can do: Beware what you click. Put basic defenses in place. Your computer should not be on the internet unless it has a firewall, anti-malware, and intrusion protection.”
“The greatest threat is the user itself and lack of education,” Laliberte added. “No matter what protection you have, the end user is the last line of defense.”
